If you want to know what is RDP gateway, and how to configure it on a Windows server, you need an ultimate guide to cover all your questions in this field.
RDP gateway allows you to increase your windows server security and lets you feel free in a crowd of attacks and security risks.
However, weak passwords, encryption methods, and ineffective controls make RDP Gateway vulnerable to malware and ransomware.
If you are relying on remote desktop access, let’s add strong cybersecurity controls to protect remote working as much as possible.
 Need a Remote Desktop?
Need a Remote Desktop?
Reliable, high-performance RDP servers with 99.95 uptime. Take your desktop on the go to all the major cities in the US, Europe, and Asia.
Get an RDP ServerWhat is RDP Gateway?
RDP gateway defines as a remote desktop gateway server that filters the RDP connections from external resources.
This Gateway will refine all incoming RDP access to the private or organization Remote Desktop server to boost your network security through making RDP secure encrypted connections.
This filtering for security enhancement establishes a point-to-point remote desktop connection to access your system.
![Best RDP provider[Top 10 RDP Server Provider 2022]](https://cloudzy.com/wp-content/uploads/Best-RDP-provider-2022-1-300x167.png)
How To Set Up RDP Gateway Server Role on Windows Server?
First things first, you have to establish an SSL certificate from your Internal CA.
1. Install the certification authority
Note: Log in with the Enterprise Admins group and the root domain’s Domain Admins group.
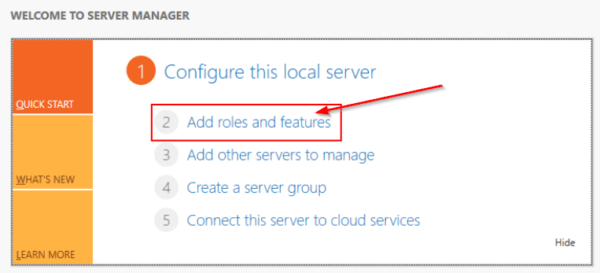
- Open the server manager, then click Add Roles and Features. The Wizard appears.
- On the Before You Begin page, click Next.
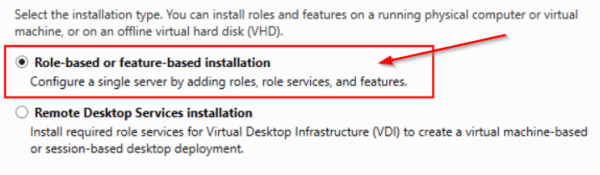
- The Role-Based or feature-based installation needs to be checked in Select Installation Type, then click Next.
- The option “Select a server from the server pool” should be checked in the Select destination server
- Select “Active Directory Certificate Services “In Select Server Roles. After that, click Add Features, and then on Next.
- Read the information, In Active Directory Certificate Services, and then click Next.
- Click Install to verify the installation
- When the installation is finished, click Configure Active Directory Certificate Services on the destination server.
- Read the credentials for the Enterprise Admins group account, and then click Next.
- Click Certification Authority in Role Services and then Next
- Select “verify that Enterprise CA” On the Setup Type page and then Next
- Confirm the Root CA, and click Next.
- Confirm “Create a new private key “on the private key page, and then click Next.
- Click Configure to apply and close the selections.
- On the Cryptography for CA page, keep the default settings for CSP (and the hash algorithm (SHA2), and consider the key length character
- keep the default setting of 2048 and then click Next.
- On the CA Name page, go on with the common name for the CA
- You need to make sure that the CA name is compatible with your conventions name and purposes, click Next.
- On the Validity Period page, in Specify the validity period, type the number and determine a time value. Click Next.
- In Specify the database locations on the CA Database page, select the folder location for the certificate database and the certificate database log. Click Next.
Also Read: How to send Ctrl+Alt+Del in RDP?
To Install Remote Desktop Gateway role service from server manager
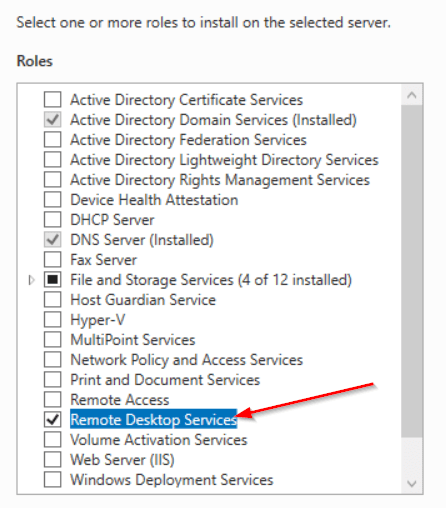
- Go to Server Manager and install the Remote Desktop Services role
- After that, the setup is completed, open Remote Desktop Gateway Manager
- In the policy section, create your authorization policy
 Need a Remote Desktop?
Need a Remote Desktop?
Reliable, high-performance RDP servers with 99.95 uptime. Take your desktop on the go to all the major cities in the US, Europe, and Asia.
Get an RDP Server2. How to make your connection and authorization policy?
- Navigate to remote desktop gateway manager to specify the allowed users
- Expand the left panel “name> Policies> Connection authorization policies.”
- Then from the right part of the window, “Create a new policy>Wizard.”
- A window for “Wizard for creating new authorization policies comes up
- Continue with the selected option “Create a policy for authorization of remote desktop connections and authorization of remote desktop resources.”
- Then click “Next.”
- Now enter a suitable name for your connection authorization policy
- Then choose a great “authentication method – password.”
- Note: you can add groups to connect this RDP gateway by clicking the “Add Group.”
- Click on “Additionally” In the group selection window
- Click on “Search” and find “Administrators of the domain” and then OK
- Choose “Enable device redirection for all client devices” and click “Next.”
- Specify the timeout and downtime and session time values and click “Next.”
- Click “Next” to finish the settings
- Type a policy name and click “Next”
- The next step is to make a group membership skip it and click “Next.”
- Select the user groups for RDP access and then press the” Overview.”
- Select “additionally”
- In the opened window, click the “Search” button and find “Domain controllers” in the result window
- Click “OK”
- Check the selected items and click “OK.”
- Click “Next”
- Select “Allow the connection only to port 3389.”
- Click “Done”
- Confirm the policy creation by clicking on the “Close” button
- Click “OK”
Also Read: How to enable RDP in Windows server 2016?
3. How to Configure the RDP Client to Talk to RDP Gateway?
To configure the RD Gateway role, you need to follow the below steps:
- Head over to the Server Manager, then choose Remote Desktop Services.
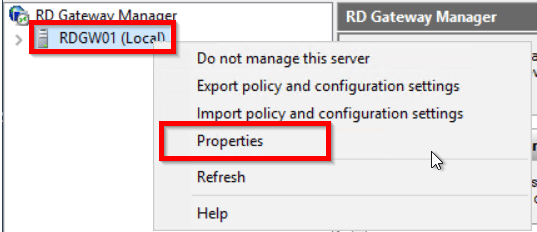
- Go to Servers on the left panel, right-click on the server name, and select “RD Gateway Manager”.
- In the RD Gateway Manager window, right-click on your gateway name, then select “Properties.”
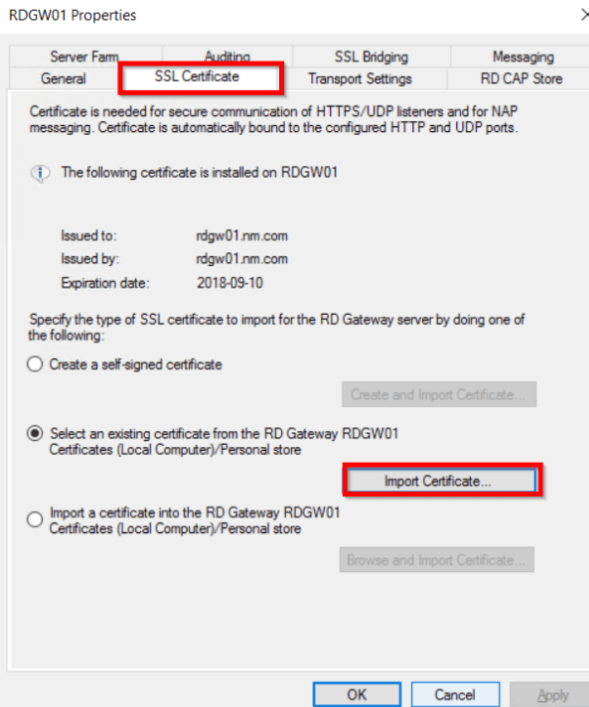
- Open the SSL Certificate tab, select the “Import Certificate,” then select Browse and Import Certificate.
- Import the SSL certificate to the client devices for establishing remote desktop gateway windows 10.
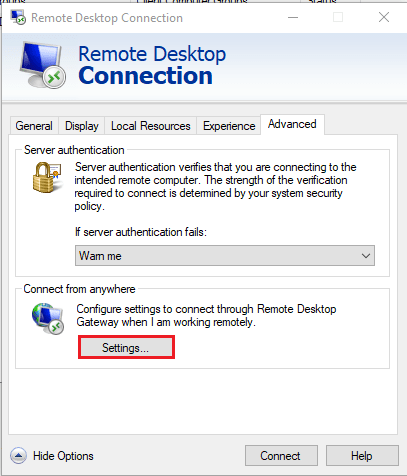
- On the client-side, Run “mstsc” and then navigate to the Advanced tab and click Settings to configure Gateway.
- Enter the external RD Gateway server FQDN.
- After the certificate import process and the private key, the certificate’s attributes will materialize.
5 useful benefits of using RDP Gateway
Using RDP Gateway have several advantages for you, but we will point out the 5 most important things that you may need to know.
1. Provides certificate authentication and MFA on an RDP gateway
Multi-factor authentication plus certificate authentication play a critical role fr the RDP gateway efficiency and performance. UserLock MFA will do this; all RDP connections transit from a gateway can be prompted for MFA either you can consider only RDP connections that originate from outsourcing the network are to be challenged with MFA.
2. There is no need to VPN
RDP clients can connect to the RDP server without VPN access. It means that the RDP gateway scales the secured RDP access for businesses. In this way, the RD Gateway makes it unnecessary to connect your company network with a VPN and only allows a specific resource to be accessed.
3. Make a reliable connection
SSL certificate guarantees the security of your connections by using encrypted algorithms for data transfer on the Internet. This is a reliable way to make the best protection from hacking attempts and attacks.
4. RDP gateway includes as a service in Windows server
The excellent point with the RDP gateway is that it is a built-in service available on the Windows server that you can take advantage of this capability without using much time and effort.
5. One connection many connections
One connection is everything in remote desktop server access. It acts as an interface that connects your employees or other clients to connect their workspace simultaneously with a high-security option remotely.
How can I buy RDP?
When it comes to Remote Desktop access and Gateway, nobody out there really helps you what to consider when deciding to choose the best RDP server.
Now, you can buy cheap RDP that offers top Remote Desktop Server Solutions with high server security and resource contention.
The nice thing is that we consider a variety of plans with different resources for any budget. It definitely makes things a lot easier to find a plan that fits your needs, and if you don’t, you can stay in touch with us to ask for a customized plan.
 Need a Remote Desktop?
Need a Remote Desktop?
Reliable, high-performance RDP servers with 99.95 uptime. Take your desktop on the go to all the major cities in the US, Europe, and Asia.
Get an RDP ServerConclusion
So, “what is RDP gateway” drives us to this vast mission to get into the details of its configuration and advantages.
SinceMicrosoft RDP gateway is one of the most notable roles of Microsoft Windows enables users to control a remote physical machine or virtual machine on the Internet. Countless professional companies are running RDP gateway to make Remote resources available with a secure connection.




![How to Make a Modded Minecraft Server? 👾 [2024 Guide]](https://cloudzy.com/wp-content/uploads/How-to-Host-a-Modded-Minecraft-Server-1-420x234.png)





Does the RDP gateway need CAL license?
How can I figure out how many users are connected to the RDPGateway at the same time?
What is the main use of RD Gateway?
Thank you for this amazing article I had never heard of RDP Gateway, it was informative.
I believe this is much like connecting through RDP directly and just changing the port that it uses through the registry, but this is my opinion I do not know how much true it is